Hi there,
I am new to the forum and have running self hosted instance of version 8.9. I am having issues getting SAML working to use FusionAuth as the idP.
My .env.local is:
AUTH_TYPE=saml
SAML_USERNAME_ATTRIBUTE='urn:oasis:names:tc:SAML:1.1:nameid-format:emailAddress'
SAML_USE_ATTRIBUTE_FRIENDLY_NAME=false
SAML_IDP_ENTITY_ID='http://localhost:9013/samlv2/ee0d98b5-0d7c-11f1-8200-364d3bfc89af'
SAML_IDP_SSO_URL='http://localhost:9013/samlv2/login/ee0d98b5-0d7c-11f1-8200-364d3bfc89af'
SAML_IDP_SLO_URL='http://localhost:9013/samlv2/logout/ee0d98b5-0d7c-11f1-8200-364d3bfc89af'
SAML_IDP_X509CERT='MII.......<SHORTENED FOR POST>'
SAML_SP_ENTITY_ID='http://localhost/saml/login'
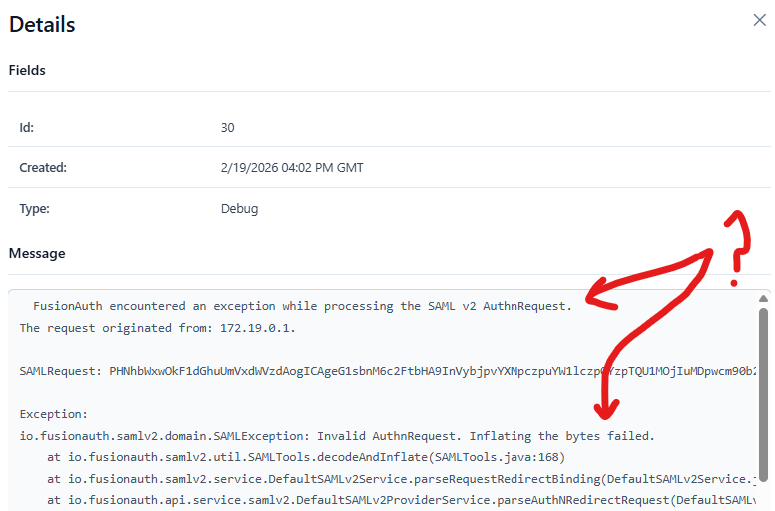
I am being redirected to the idP but FusionAuth is throwing an error that the AuthnRequest is invalid:
If I use the OneLogin validation tool the request seems to be valid though.
It is worth pointing out that I have tried numerous versions of FusionAuth and we have a SAML integration working with Adobe Commerce from FusionAuth so am pretty confident that this is OK.
The AuthnRequest XML is:
<samlp:AuthnRequest
xmlns:samlp="urn:oasis:names:tc:SAML:2.0:protocol"
xmlns:saml="urn:oasis:names:tc:SAML:2.0:assertion"
ID="ONELOGIN_9b5743f10f44e4ec43dce285674b5caef1a4ea3e"
Version="2.0"
ProviderName="Example"
IssueInstant="2026-02-19T14:07:51Z"
Destination="http://localhost:9013/samlv2/login/ee0d98b5-0d7c-11f1-8200-364d3bfc89af"
ProtocolBinding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST"
AssertionConsumerServiceURL="http://localhost/saml/acs">
<saml:Issuer>http://localhost/saml/login</saml:Issuer>
<samlp:NameIDPolicy
Format="urn:oasis:names:tc:SAML:1.1:nameid-format:unspecified"
AllowCreate="true" />
</samlp:AuthnRequest>
and the SAML metadat from fusionauth is:
<ns2:EntityDescriptor xmlns="http://www.w3.org/2000/09/xmldsig#" xmlns:ns2="urn:oasis:names:tc:SAML:2.0:metadata" xmlns:ns3="http://www.w3.org/2001/04/xmlenc#" xmlns:ns4="urn:oasis:names:tc:SAML:2.0:assertion" entityID="http://localhost:9013/samlv2/ee0d98b5-0d7c-11f1-8200-364d3bfc89af" ID="_ee0d98b5-0d7c-11f1-8200-364d3bfc89af">
<ns2:IDPSSODescriptor WantAuthnRequestsSigned="true" protocolSupportEnumeration="urn:oasis:names:tc:SAML:2.0:protocol">
<ns2:KeyDescriptor use="signing">
<KeyInfo>
<X509Data>
<X509Certificate>MIIC........SHORTENED_FOR_POST</X509Certificate>
</X509Data>
</KeyInfo>
</ns2:KeyDescriptor>
<ns2:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="http://localhost:9013/samlv2/logout/ee0d98b5-0d7c-11f1-8200-364d3bfc89af"/>
<ns2:SingleLogoutService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="http://localhost:9013/samlv2/logout/ee0d98b5-0d7c-11f1-8200-364d3bfc89af"/>
<ns2:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-Redirect" Location="http://localhost:9013/samlv2/login/ee0d98b5-0d7c-11f1-8200-364d3bfc89af"/>
<ns2:SingleSignOnService Binding="urn:oasis:names:tc:SAML:2.0:bindings:HTTP-POST" Location="http://localhost:9013/samlv2/login/ee0d98b5-0d7c-11f1-8200-364d3bfc89af"/>
</ns2:IDPSSODescriptor>
</ns2:EntityDescriptor>
Any help would be appreciated or suggestions on what I am doing wrong.
Has anyone else done an implementation using FusionAuth as the Identity Provider?