I need little assistance on integrating LDAP-Authentication to SuiteCRM 8.2 b2 running on Debian 11. ActiveDirectory is provided by Samba.
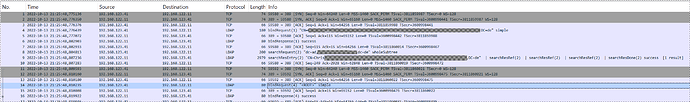
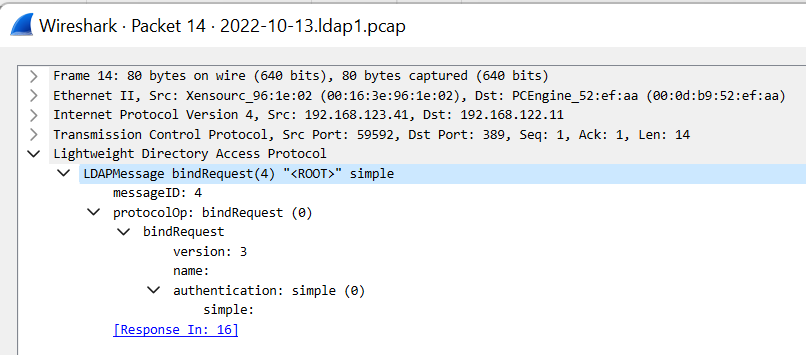
Configuration of LDAP-Provider seems fine as Network Trace shows authenticated ldap_bind with following ldap-search for the User-Object trying to log on in Browser. Search successfully returns exactly one LDAP-Object.
Thereafter, Network Trace shows another ldap_bind (this time without authentication) and some searches (for Example to Context “Configuration”) - all failing because of the missing ldap authentication.
In my understanding, in second step SuiteCRM should ldap_bind authenticated as LDAP_SEARCH_DN / LDAP_SEARCH_PASSWORD, search for LDAP_QUERY_STRING beginning in LDAP_DN_STRING. Exactly one LDAP-Object should be found which is used to do another ldap_bind using the Password given from User in Browser.
It is not an Option to me to allow unauthenticated ldap_search. For Debug only, I changed from LDAPS to LDAP.
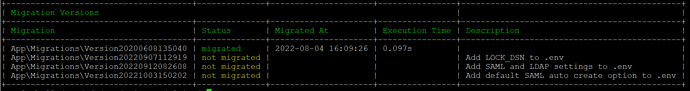
Maybe I missunderstood the LDAP Configuration Params? They are as follows:
.env.local
###> AUTH_TYPE ###
#AUTH_TYPE=native
AUTH_TYPE=ldap
###< AUTH_TYPE ######> LDAP CONFIG ###
LDAP_HOST=‘192.168.xxx.11’
LDAP_PORT=389
LDAP_ENCRYPTION=‘none’
LDAP_PROTOCOL_VERSION=3
LDAP_REFERRALS=false
LDAP_DN_STRING=‘dc=ad,dc=xxxxxxxxxxxxx,dc=de’
LDAP_QUERY_STRING=‘(sAMAccountName={username})’
LDAP_SEARCH_DN=‘CN=xxxxxxxxxxxxxx,dc=ad,dc=xxxxxxxxxxxxx,dc=de’
LDAP_SEARCH_PASSWORD=‘xxxxxxxxxxxx’
###< LDAP CONFIG ######> LDAP AUTO CREATE CONFIG ###
LDAP_AUTO_CREATE=enabled
LDAP_PROVIDER_BASE_DN=‘dc=ad,dc=xxxxxxxxxxxxx,dc=de’
LDAP_PROVIDER_SEARCH_DN=‘CN=xxxxxxxxxxxxxx,dc=ad,dc=xxxxxxxxxxxxx,dc=de’
LDAP_PROVIDER_SEARCH_PASSWORD=‘xxxxxxxxxxxx’
LDAP_PROVIDER_DEFAULT_ROLES=ROLE_USER
LDAP_PROVIDER_UID_KEY=‘sAMAccountName’
LDAP_PROVIDER_FILTER=‘(&(sAMAccountName={username})(objectcategory=person)(objectclass=user))’
###< LDAP AUTO CREATE CONFIG ##
May somebody push me to the right direction? Any hint appreciated!
Regards…
Chris